mirror of
https://github.com/louislam/uptime-kuma.git
synced 2026-03-02 22:57:00 -05:00
Ping stopped working with Debian base on Podman #216
Labels
No labels
A:accessibility
A:api
A:cert-expiry
A:core
A:dashboard
A:deployment
A:documentation
A:domain expiry
A:incidents
A:maintenance
A:metrics
A:monitor
A:notifications
A:reports
A:settings
A:status-page
A:ui/ux
A:user-management
Stale
ai-slop
blocked
blocked-upstream
bug
cannot-reproduce
dependencies
discussion
duplicate
feature-request
feature-request
good first issue
hacktoberfest
help
help wanted
house keeping
invalid
invalid-format
invalid-format
question
releaseblocker 🚨
security
spam
type:enhance-existing
type:new
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/uptime-kuma#216
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @Eskander on GitHub (Sep 10, 2021).
Is it a duplicate question?
No
Describe the bug
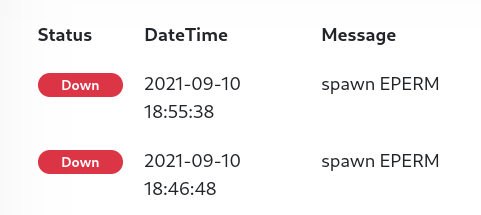
Monitoring using Ping stopped working with error
spawn EPERMafter pulling latest Docker image 1.6Public domains like
google.comor IP addresses didn't work either.Reverting back to the Alpine base with
uptime-kuma:alpinefixed the issue.I'm also using HTTP and TCP monitoring and they work as expected.
To Reproduce
Expected behavior
Monitoring using ping should resolve correctly.
Info
louislam/uptime-kuma:latestScreenshots
Error Log
@louislam commented on GitHub (Sep 10, 2021):
Strange, it is working is my side.
@louislam commented on GitHub (Sep 10, 2021):
"ping" command is missing in your side, but I don't know why, because we should be using the same docker image.
@Eskander commented on GitHub (Sep 10, 2021):
@thespad commented on GitHub (Sep 10, 2021):
It's probably a selinux issue as you're running fedora. I'd check the selinux logs on the host to see if it's blocking the ping execution.
@Eskander commented on GitHub (Sep 10, 2021):
I also suspected SELinux at first, and set it to permissive but nothing changed. Also that wouldn't explain why Alpine worked but Debian didn't.
It does appear to be a permission issue though:
@thespad commented on GitHub (Sep 10, 2021):
Alpine and Debian ship very different ping binaries, not least because of glibc vs muslc, so it's not that odd for it to work in one but not the other
@louislam commented on GitHub (Sep 10, 2021):
Looks like your issue
https://github.com/mviereck/dockerfile-x11docker-deepin/issues/19
I wanna cry again😂
@louislam commented on GitHub (Sep 10, 2021):
I can reproduce the problem with
--cap-drop=net_rawI don't know what to say, but yeah... come on, it is the simplest command
pingin linux, how could it fail....@Eskander commented on GitHub (Sep 10, 2021):
Can confirm! the following fixed the issue:
I can submit a PR to add it to documentation if required.
I'm still curious about why it worked it Alpine though, how does it bypass the permission..
@louislam commented on GitHub (Sep 10, 2021):
If I set
cap-drop=net_rawon alpine, it is not working too in my side.Another question is, I actually tested on Ubuntu, Centos 7, AlmaLinux, Oracle Linux. They are working without NET_RAW.
Is it related to Docker version? My docker version is 20.10.8, installed with official guide.
@thespad commented on GitHub (Sep 10, 2021):
NET_RAW is one of the default caps in docker, see here, so you shouldn't need to add it explicitly.
@Eskander commented on GitHub (Sep 10, 2021):
Aha my bad! I'm actually using rootful Podman as a docker replacement with
podman-docker, I should've mentioned it from the start. It probably comes down to differences in default capabilities.I edited my original post for whoever ends up in the same situation.
@danielo515 commented on GitHub (Mar 9, 2022):
Hey, not sure if I should open a new issue or not.
If I add this option to my docker-compose:
Ping related checks fails because permissions. Is there any way I can keep that option (for security reasons) but still allow ping? I tried adding cap-add but that doesn't seem to work
@thespad commented on GitHub (Mar 9, 2022):
Unlikely, I expect ping has suid set to enable it to run without you having to run the container as root. No new privs will stop suid from working, by design.
@danielo515 commented on GitHub (Mar 9, 2022):
Sorry, I don't understand your answer completely. What is unlikely? being able to cap no new privs and being able to execute ping because it uses suid?
@thespad commented on GitHub (Mar 9, 2022):
It's unlikely that you'll make it work with
no-new-privileges:truebecause that prevents elevation of the account, and if ping has suid set to allow elevation so that a non-root user can run it, thenno-new-privileges:truewill prevent that from working.@Jackbennett commented on GitHub (May 6, 2025):
For some reason updating an older 1.x to 1.23.16 didn't have a problem but moving to v2.0.0-beta.2 triggered this. Adding
--cap-add=NET_RAWto my rootless podman exec in the user service unit file sorted out the spawn EPERM.