mirror of
https://github.com/dani-garcia/vaultwarden.git
synced 2026-03-02 22:57:18 -05:00
[META] Feature Requests #123
Labels
No labels
SSO
Third party
better for forum
bug
bug
documentation
duplicate
enhancement
future Vault
future Vault
future Vault
good first issue
help wanted
low priority
notes
question
troubleshooting
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/vaultwarden#123
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @dani-garcia on GitHub (Nov 9, 2018).
To avoid cluttering the issue tracker with feature requests, please comment any requests here and we'll keep a list.
When available, I've linked a related issue or comment to add context to the request.
Authentication
Database support
Admin page
/admin/diagnosticsSecurity
Lock accounts after X login failures, configurable.(Rate limiting is a better option, else this would give people with bad intentions the option to lock everybody out from the specific vault)Either by documentation using third party tools, firewall, reverse proxy etc.. Or maybe built in without to much hassel #723
Docker images
Other
My Itemssupport as documented here https://bitwarden.com/blog/bring-complete-reporting-and-centralized-control-to-your-organization-vault/ (See: #6579 )/api/accounts/delete-recoverwith{"email":"provided@email.address"}param(Partially added to support Bitwarden Directory Connector v2022.11.0)
third-partydepends on Rocket support) (See: #685 / #2917) (Added via #3404)If anyone wants to help implementing these features, we are available here or on the matrix channel to help guide you as much as we can.
@quthla commented on GitHub (Dec 22, 2018):
What is needed for #241? Seems somebody already posted the needed changes in the corresponding issue so that could maybe be integrated?
@dani-garcia commented on GitHub (Dec 22, 2018):
Yes, someone would have to check those changes, see what can be integrated into the project directly (possibly a config option for the mount point) and create the documentation on how to configure the vault, proxy, etc.
@mprasil commented on GitHub (Jan 15, 2019):
@dpffxhad added it to the list
@Peneheals commented on GitHub (Jan 16, 2019):
It would be great to see an (admin) feature which can help sysops to test mailing functionality. Maybe somewhere a button which can send a test e-mail to the actual user's address and which gives back a fail/success message after the action.
@mprasil commented on GitHub (Jan 16, 2019):
Good idea @Peneheals, @njfox what do you think?
@p-rintz commented on GitHub (Jan 16, 2019):
Would it be possible to introduce 2FA auth to the /admin panel as well?
@njfox commented on GitHub (Jan 16, 2019):
I also think that's a good idea, and it shouldn't be too difficult to implement. I can look at adding the necessary API endpoints once I find some time, or knowing @dani-garcia he'll probably get to it first
@dani-garcia commented on GitHub (Jan 16, 2019):
About 2fa:
To do this, we'll need to implement it separately from the already existing 2fa code. I'm not sure if for this case it's worth it to implement multiple 2fa systems, so I would think just totp and maybe email would be good enough.
That said, this would require some changes to the admin page to input the 2fa code: we can't just ask for it at the start because it changes every 30 seconds .
Edit: About the email, as a workaround, you can invite yourself to test if it works for now, but it would be great to add
@chinenual commented on GitHub (Feb 1, 2019):
I am having trouble getting an Apache reverse-proxy to work in my organization. For various reasons, I can't create a new subdomain for bitwarden - i need to run it as https://my.proxy.domain/bitwarden forwarding to localhost running http on a non-standard port. However I cannot find a way to get Apache's mod_proxy to proxy from /bitwarden context to root context. For other applications I'm able to create proxies to as long as the target application uses a non-root context.
I.e. I want to do this:
https://my.proxy/bitwarden <-> http:/localhost:1234
I can get other apps to work if the internal app uses non-root context -- e.g.
https://my.proxy/acontext <-> http:/localhost:1234/anothercontext
Can bitwarden_rs be configured to listen to /bitwarden_rs or /bitwarden instead of / ? If not, can someone help in constructing apache mod_proxy / mod_rewrite rules to proxy the bitwarden_rs root context from a non-root proxy context?
@mprasil commented on GitHub (Feb 2, 2019):
@chinenual see #71. The TL/DR is that while bitwarden_rs doesn't mind serving from a sub path, client apps don't support that. There was some effort modifying the Vault code to allow this, but I haven't seen anyone reporting that they got it working.
@chinenual commented on GitHub (Feb 2, 2019):
Thanks @mprasil - I'll keep my eye on upstream client support and check back here if/when it's supportable.
@quthla commented on GitHub (Feb 2, 2019):
@mprasil I think only the web vault needs some patching (which has already been done?)
https://github.com/dani-garcia/bitwarden_rs/issues/241#issuecomment-436373392
I changed the path in the android app and it'll correctly call api at that path.
"POST /bw/api/accounts/prelogin HTTP/1.1"
@mprasil commented on GitHub (Feb 3, 2019):
Good to know @quthla, are you sure all functionality is present in the mobile client apps - like attachments. (also this probably still rules out using the official desktop app?)
@pdarcos commented on GitHub (Feb 21, 2019):
Awesome project guys!
+1 for Postgresql and/or MariaDB support.
@pdarcos commented on GitHub (Feb 24, 2019):
Also +1 for groups support. I know you can use organiztions as a workaround but it is an unwieldy solution. Native support for groups would be fantastic.
@tcjew commented on GitHub (Feb 25, 2019):
support for rqlite! Bassicly a sqlite database with synchronization support across multiple servers.
As i am looking for a redundant solution
@pdarcos commented on GitHub (Feb 26, 2019):
Push notifications would be cool too. I know you'd have to compile your own mobile clients for them to work but that's not such a big deal and having all your devices synced is very useful IMO.
I also like the focus on security. The option to force 2FA for all logins would make it super secure. It can be problematic letting users water down the security and effectively negating 2FA. Most people - surprisingly even informed ones - tend to choose convenience over security.
@ta-vroom commented on GitHub (Mar 16, 2019):
Support for custom icons? I was able to add missing icons for locally hosted sites and I'm pretty sure you could override domain icons, but what about separate icons for multiple accounts?
For customizing icons, in /data/icon_cache you can change the icons. Icons for missing domains have a *.miss extension. Copy a png file to that directory without the *.miss extension and it should render normally in the vault.
@dani-garcia commented on GitHub (Mar 16, 2019):
To support custom icons per cipher instead of as it is (per domain) we would probably need the clients to support them. As a possible workaround, you could create a fake invalid URL for the first URL field, like
-mycustomicon1.comand use the other URL fields for the actual URL. With that you could move your custom icon to/data/icon_cache/-mycustomicon1.com.pngand it should work.Note that if you are going to keep custom icons, you should set
ICON_CACHE_TTLto 0 to disable the server from renewing them in 30 days.@mprasil commented on GitHub (Mar 16, 2019):
To expand on what @dani-garcia said above, the icons API isn't authenticated. The client just asks icon for a domain and that's all information we'll get. This is why we don't know which user is requesting the icons.
@ThiefMaster commented on GitHub (Mar 23, 2019):
It would be nice to have the "new device logged in" emails like in the original service:
@ThiefMaster commented on GitHub (Mar 23, 2019):
Why can't they use the push.bitwarden.com push proxy instead of requiring people to compile their own apps? If you consider it unethical, just add a statement that people should buy premium before enabling it.
@mprasil commented on GitHub (Mar 23, 2019):
@ThiefMaster is there some information about how this endpoint can be used? I've got the impression that there are some credentials needed.
@ThiefMaster commented on GitHub (Mar 23, 2019):
It looks like all you need is a key from https://bitwarden.com/host/
github.com/bitwarden/server@255855887b/src/Core/Services/Implementations/RelayPushRegistrationService.cs (L23)@Kovah commented on GitHub (Mar 25, 2019):
Hello there. First of all many thanks for this implementation of Bitwarden! 💯
Everything is working fine but I would like to ask for two smaller things:
Both would be quite helpful to get (non-english speaking) family members to use Bitwarden. (If it's possible already I would like to know how, couldn't find any options for this.)
@mprasil commented on GitHub (Mar 25, 2019):
Not sure if I follow you there @Kovah. Where would you like to change this? The only place I can think of are the emails - you can provide your own translated templates there.
I don't think this saved or provided by the server anywhere. The setting is saved client side and as far as I know the default follows your system settings.
@dani-garcia commented on GitHub (Mar 25, 2019):
The users return a hardcoded Culture value of en-US at the moment, but I'm not sure if that affects the clients.
@Kovah commented on GitHub (Mar 25, 2019):
Where would I do that? Also, it's on the login pages. Would be nice to have the own name there.
About the language thing: this would be only needed for the login page / registration form. Just tested this by changing my system language and it's set automatically. So nothing to do here. :)
@mprasil commented on GitHub (Mar 26, 2019):
Ah so you're talking about
Bitwarden, notbitwarden_rs? I think you might need to recompile the vault code with your changes patched in to do that. We just use more-less direct code from upstream for that part. If you decide to do that, you can point to your version of vault viaWEB_VAULT_FOLDER.As for the templates, you can see the built-in ones here. You can modify them and mount them somewhere inside the container and then point
TEMPLATES_FOLDERthere.@ViViDboarder commented on GitHub (Apr 15, 2019):
LDAP syncing has been added to the wiki: https://github.com/dani-garcia/bitwarden_rs/wiki/Syncing-users-from-LDAP
@mprasil commented on GitHub (Apr 16, 2019):
Can we mark the LDAP thing done or is there something else that needs to be done?
@ImNtReal commented on GitHub (Apr 16, 2019):
Does the LDAP Synching feature simply lookup users in a LDAP directory, and send them invitation e-mails? What I was hoping for was using LDAP as an authentication backend, so that users have the same credentials to login to bitwarden_rs as they do everything else on my network that uses LDAP for authentication.
@dani-garcia commented on GitHub (Apr 16, 2019):
@mprasil I think we can at mark it as done, but indicate that the official ldap connector app is not supported, maybe we can add that as a separate feature.
@ImNtReal Yes, that's exactly the same thing the upstream connector app does, it just adds and removes users, but the users need to exist beforehand. I'm not sure how LDAP works internally but I imagine the passwords are hashed, so we don't have a way to get their current password to create them an account.
@mprasil commented on GitHub (Apr 16, 2019):
@dani-garcia I've updated the issue and added a sub-task to support the official thing. Although right now @ViViDboarder's solution is probably covering most of the functionality..
@RomanHargrave commented on GitHub (Apr 16, 2019):
Correct, and in most directory configurations I do not believe you will be able to retrieve the hashes.
One way to deal with the want to authenticate users via directory works much like Bitwarden works today, requiring a user-held secret to decrypt the vault -
Upon a new user signing in successfully, the password they entered is used to generate the vault key.
To handle password changes, if a user signs in successfully but the derived key does not match that which was used to encrypt their vault, they would be asked to enter their old password and the vault would be re-encrypted in the same manner that a password change works now.
Unfortunately, implementing this would break compatibility with Bitwarden.
@kennylevinsen commented on GitHub (May 2, 2019):
We could contribute equivalent functionality upstream, in order to keep us in sync. It would also aid upstream in obtaining proper directory support.
@bremensaki commented on GitHub (May 6, 2019):
Is there a way to override the default organisation name from "bitwarden_rs" in the invitation emails that I'm missing, or is this something that'd be covered under the "better email templates" list item?
@mprasil commented on GitHub (May 8, 2019):
@bremensaki You can provide your own template for emails, would that work for you?
@kreativekrise commented on GitHub (May 23, 2019):
It would be nice to implement the possibility to use docker secrets, e.g. for the ADMIN_TOKEN environment variable.
Here you will find a nice article how you could implement it: https://medium.com/@adrian.gheorghe.dev/using-docker-secrets-in-your-environment-variables-7a0609659aab
@mprasil commented on GitHub (May 23, 2019):
@KreativeKrise, makes me wonder if we can just create symlink from
/.envthat is read at startup to/run/secrets/bitwarden_rs_secrets. We'd add something like this into the Dockerfile:If there's no secret the service starts as usual, if you mount your own .env file, it will override the symlink, so that is still going to work as expected. Now to create the docker secrets, you'd do something like:
basically adding all passwords into one docker secret. That way there's no need for startup wrapper script, that we might want to then drop somehow if we want to go for distroless based image.
@ViViDboarder commented on GitHub (May 23, 2019):
@KreativeKrise can't you already store your configuration in a file and mount that using Docker Secrets?
Also you can do what that blog suggests already without an upstream patch. This is one of the cool things about how Docker layers work.
The
CMDin the Dockerfile is set to just run the bitwarden executable. So you could build your own Dockerfile that looks something like this:Disclaimer: I haven't tested this, there may be small errors, but the gist is the same
Where
entrypoint.shis something like:And your secrets file is something like:
@Pschittt commented on GitHub (Jun 18, 2019):
Here a few features requests :
@mprasil commented on GitHub (Jun 19, 2019):
@Pschittt
docker save) as an fallback? It's quite small.@Pschittt commented on GitHub (Jun 19, 2019):
@mprasil
@mprasil commented on GitHub (Jun 19, 2019):
@Pschittt as for 2) see #504, there isn't much we can do server side as most of the data is client-side encrypted. There are some ideas how to achieve this, but it would most likely be external project rather than being part of bitwarden_rs.
@stripe4 commented on GitHub (Jul 21, 2019):
An option not to show organization credentials in "My Vault". Currently it's difficult to separate my private credentials from organization ones.
Ability to add picture logos to organizations.
@mprasil commented on GitHub (Jul 22, 2019):
@stripe4 I think both of these will need to be implemented on the client side, so you need to make the request upstream. (In their forums)
@onggie commented on GitHub (Aug 7, 2019):
Hi, are we likely to see the support of the official director connector any time soon?
@dani-garcia commented on GitHub (Aug 8, 2019):
It would depend on a third party helping with a PR, as I don't have neither the knowlege nor a server to work with LDAP.
@H3npi commented on GitHub (Aug 23, 2019):
it would be awesome to implement a simple Healthcheck to the Dockerfile.
@dani-garcia commented on GitHub (Aug 23, 2019):
We have the
/aliveendpoint that could be used to handle that check:We’d also have to handle the case where HTTPS is enabled though.
@tckb commented on GitHub (Oct 29, 2019):
I would love to see a native backup and restore solution. currently, I am running this on k8s and it would be pretty cool to have a native backup cron of sorts running in bg
@ViViDboarder commented on GitHub (Oct 29, 2019):
@tckb there are other containers you could attach to Bitwarden_rs for backups. I'm using images that I built for Duplicity and Restic for doing exactly what you're talking about.
Both allow you to set up cron schedule for both backups and verification. They also allow automatically restoring when the data directory is empty. Backing up a database requires a pre-backup and a post restore script.
Here's the gist of it in a gist of it... https://gist.github.com/ViViDboarder/aa480ac3411f359df80376023bc4e987
To make things simpler, I should probably have tagged images for backing up sqlite and mysql with scripts bundled.
@tckb commented on GitHub (Oct 29, 2019):
thanks for the cue! @ViViDboarder I am thinking of setting up a k8s cron job. and container which does the backup. the k8s cron is especially makes easy to change the schedule in demand w/o needing to the build image.
@ViViDboarder commented on GitHub (Oct 29, 2019):
@tckb wow. I really ought to switch to k8s, hah. That's super handy.
I've been using Dockron to get something similar (cron schedules to update my ddns and renew certs), but I had already built the self contained backup images. The one advantage to the all-in-one images that I shared is that it contains restoration as well. If just running backups on cron, you won't be able to automate restoration should you re-deploy on a different host. You may not care so much about this though.
With the embedded cron images linked, you don't actually have to rebuild the image to change schedule, just update the env variable and restart the container. The Dockerfile and image are only built to add the sqlite executable.
@tckb commented on GitHub (Oct 29, 2019):
@ViViDboarder that looks interesting, are you running it in swarm? btw, http://duplicity.nongnu.org looks pretty good fit for something I am searching. Which provider are you using for storage?
@ViViDboarder commented on GitHub (Oct 29, 2019):
@tckb for now just Docker Compose directly on each host and I use Ansible to orchestrate.
I'm using Backblaze B2 for storage. It's convenient and affordable. Both Duplicity and Restic support many backends though.
@ntimo commented on GitHub (Nov 14, 2019):
I would like to suggest to add a configurable rate limit to the API https://github.com/dani-garcia/bitwarden_rs/issues/723.
@tckb commented on GitHub (Nov 14, 2019):
@ntimo you an have rate limiting on the proxy. I have it configured via Nginx proxy
@ntimo commented on GitHub (Nov 14, 2019):
@tckb Yes you could do it with a reverse proxy, but I personally think it would be better if the API would handle this by itself.
@ajwstevens commented on GitHub (Nov 25, 2019):
Hello, I was wondering if it's possible to search through the securenotes? I think this is possible in upstream: https://help.bitwarden.com/article/searching-vault/ In bitwarden_rs I made a secure note with the string "imanager' in it. When i search through the vault I would like that note to pop up.
@dani-garcia commented on GitHub (Nov 25, 2019):
@ajwstevens That works for me but you need to use the special syntax:
You might need to add asterisks as wildcards:
It's all documented in the section Advanced searches of the link you posted.
@cedricroijakkers commented on GitHub (Dec 9, 2019):
Hi all, I would like to request a new feature: audit trail logging. Allow the possibility (with an environment variable) to log which user is accessing a password in an organisation. For auditability, we would like to see when somebody is creating, modifying, or reading a password in an organisation. No need to log access to a private password, but for shared passwords in an organisation, we would like to keep an audit trail of access, in case of abuse.
@ptman commented on GitHub (Dec 9, 2019):
@cedricroijakkers I would like that too, but think about how bitwarden works and how this would be possible. Since the passwords are synced to different devices, what forces a client to report to the server what local operations have occured?
@cedricroijakkers commented on GitHub (Dec 9, 2019):
@ptman Forgive the ignorant bliss, I'm only just starting to learn the architecture of Bitwarden, but I noticed that when opening a password in an organsation, the decription key is being downloaded from the server. Would that be a possibility?
@ptman commented on GitHub (Dec 9, 2019):
@cedricroijakkers you probably know more than me already. I just drew conclusions from there being a sync instead of each access going to the server
@nakermann1973 commented on GitHub (Dec 16, 2019):
Hi - I would like to suggest a new feature
Allow attachments to be stored in the database, instead of on the filesystem. This would make backups of the data easier, by only backup up the database, and would also allow clustering/redundancy of the server, by not having to rely on local storage.
@Nonobis commented on GitHub (Jan 1, 2020):
Hi,
Could you add an automatic export of Key/Data as encrypted/compressed file to a targeted folder ?
For example, export to a folder backuped in cloud, if data is crypted it's not a problem.
Better if server crash :)
@yelch commented on GitHub (Jan 14, 2020):
First of all: Thank you very much! I am using the docker image on a synology with reverse proxy, letencrypt and everything (incl. push-updates) is working very well!
I have a few questions/feature requests:
Backup
Could you let us specify a backup location and add automated backups (daily/weekly) in the admin interface.
Fantastic would be a backup plan option like 'keep daily for 30 days / weekly for 6 months / monthly for a year.
Folders
What folders are needed/possible to specify. Are there only the ones specified in the Read-only section?
Customisation
Is there a dark theme planned? If I change the web-vault folder, how can I customize the interface? Is it possbile to create child-themes?
@mprasil commented on GitHub (Jan 14, 2020):
@yelch I think the Backup is somewhat inappropriate name for what should really be called DB dump. To have scheduled backups and to have some form of rotation is a functionality that your backup software should do, not a password management server.
There are couple interesting projects doing some automation around
bitwarden_rsbackups that are linked from our wiki, but generally speaking most backup software offers some form of such functionality.@SuNNjek commented on GitHub (Jan 16, 2020):
Hi,
I'm wondering if it would be possible to build an ARM Docker image with Postgres enabled?
I tried generating the Dockerfile for it, but the build fails with the linker saying it can't find libpq even though it should be installed according to the Dockerfile 😕
@Crow-Control commented on GitHub (Jan 29, 2020):
@SuNNjek
Try checking in the docker itself if the image is actually there. Somethings you need a different reference for different platforms for certain libraries.
Something like this top open a console inside the docker image:
Docker exec $image /bin/bash
@T-bond commented on GitHub (Feb 8, 2020):
Hi,
Would it be possible to get an Alpine version from the bitwardenrs/server-postgresql docker image (as the main bitwardenrs/server variant has it already)?
@alfonsrv commented on GitHub (Feb 8, 2020):
Please add the ability to export and manage organizations more in-depth. A user forgot his password and I cannot delete him because he's the owner of an organization. Also when exporting user stores, organizations cannot be optionally exported.
Also, is it possible to actually sync LDAP user passwords / authenticate users via LDAP or is this not viable due to security concerns, e.g. the way stores are en-/decrypted?
@stanelie commented on GitHub (Feb 19, 2020):
I too would like a way to authenticate against LDAP. As I understant it, the bitwarden_rs_ldap is only there to invite people from your ldap tree to your bitwarden_rs instance.
@ViViDboarder commented on GitHub (Feb 19, 2020):
It is not possible to use LDAP as the sole form of authentication without sacrificing client side decryption. At least not without completely rewriting the client applications.
I don't know if there are examples of password managers doing LDAP auth out in the wild. Even enterprise solutions like LastPass use LDAP only for provisioning/deprovisioning. https://www.lastpass.com/enterprise/directory-integration
@Crow-Control commented on GitHub (Feb 19, 2020):
@stanelie be aware you don't even actually "authenticate" against the bitwarden server afaik.
You authenticate your password in the client against a local datablob (recieved from the server), the result of which is used to authorise you access to your data on the server.
In contrast with LDAP the Bitwarden server never actually does the authentication itself.
So yes, what @ViViDboarder says: it would require a whole redesign, which would make it loose it's unique features compared to something like Nextcloud Passwords.
@stanelie commented on GitHub (Feb 19, 2020):
Thanks for kindly taking the time to explain that.
@jhf2442 commented on GitHub (Feb 21, 2020):
Hi,
hope this is the right place to issue my wishes regarding the password checking tools (weak, exposed, reused etc) :-) or is this something that should be reported to upstream "official" BW codebase ?
Many thanks
@Crow-Control commented on GitHub (Feb 21, 2020):
@jhf2442
This is formost a client side (UI) issue from Bitwarden, only after Bitwarden themselves adds this feature should/could it be added to bitwarden_rs. Bitwarden_rs doesn't maintain the clientside codebase.
This is client side only, if bitwarden adds this to the client side code, it would auto-magically also be fixed when using bitwarden_rs
Again client side only, not something related to bitwarden_rs.
Please be aware bitwarden_rs is ONLY the server side of the application. Simply put it only does the lookups in the database for the client. Everything you see and touch is mostly not a API query (Simply put: database related).
Simply put: If it grabs new data (passwords, username etc) it does a api query to the server, so in those cases its both client side (it does something you can view and interact with) and server side (it gets data).
In cases where it just sorts data differently its either just client side or a combination. (depending on coding preferences)
In cases where it's just showing weither a password is bad or not (You already have the data, just checking if its good), it's just client side.
If something has a client-side part, it can't be fixed by bitwarden_rs. As soon as bitwarden implements it it will/can be ported to bitwarden_rs.
(Yes I know this is a simplification of the API, but it's the most easy form to explain it in such a way a non-coder should be able to justify weither something is Client or Server side)
@jhf2442 commented on GitHub (Feb 21, 2020):
@Ornias1993 thanks for the extensive reply - Server-side API would have been enough :-)
I've submitted my feature requests on the pertaining forum at the bitwarden website ... looks like the 2nd one (sorting the weak passwords per status) was already filed last month !
In case people want to upvote these topics :
@alfonsrv commented on GitHub (Feb 21, 2020):
Regarding LDAP – but why wouldn't this work? We can still hold the password as is in the client application. A workflow could look like this:
Where am I going wrong? The added LDAP auth step doesn't require rewriting the client as far as I can tell(?)
@ViViDboarder commented on GitHub (Feb 21, 2020):
@alfonsrv biggest reason is password change.
You have to maintain two passwords, which will require a client change.
@alfonsrv commented on GitHub (Feb 21, 2020):
@ViViDboarder right. So an option could be a fallback interface. It could trigger as soon as authentication succeeds and bitwarden_rs realizes it cannot decrypt the keys properly, redirecting to a rudimentary interface – much like the /admin – requiring a user to input both the old and new password, in order to also facilitate the password change on the bitwarden_rs side.
@mprasil commented on GitHub (Feb 21, 2020):
@alfonsrv I think you're ignoring the core feature of Bitwarden - client side encryption. Client does not send password as entered to the server, it sends just derived key. (which is non-reversible) So the actual password never touches server.
Which also means the server can't re-encrypt anything as it does not know the password.
@ViViDboarder commented on GitHub (Feb 21, 2020):
@alfonsrv yes. That’s then two passwords anyway. Today, nothing stops you from changing your Bitwarden password to your LDAP password.
This was discussed earlier (in this thread or another), but Bitwarden_rs is only a server. We use the upstream clients. If Bitwarden proper adds this kind of functionality into their clients, we could do the same.
But again, I find it unlikely for the reasons mentioned earlier.
@Crow-Control commented on GitHub (Feb 21, 2020):
@mprasil Indeed, the whole idea is based on a flawed interprentation of how Bitwarden works:
"password is sent to server"
Which it isn't.
"Bitwarden server authenticates"
Which it doesn't, authentication is client side, authorisation is (partly) server side.
"If password is authenticated against LDAP successfully"
Nice and all, but the server has no authority weither you are or aren't authencitated, so neither would LDAP.
What could work:
In theory it would be possible to let some form of middleware propagate any LDAP password changes to Bitwarden (but not visa versa).
But that middleware wouldn't be part of Bitwarden_rs as it goes out-of-scope aka it goes against the core design philosophy of bitwarden. Simply put: The bitwarden is designed around: The server never recieves or handles your password.
It would also require client side changes (for example hiding the password change options within bitwarden), which would also be out of scope for bitwarden_rs
Using the bitwarden API, you could however very well make a form of middleware thats server agnostic. It would however be a seperate github project.
@mprasil commented on GitHub (Feb 21, 2020):
@Ornias1993 yeah you could implement something outside bitwarden, but at that stage you might be better to just use something else that doesn't do client side encryption.
@jjlin commented on GitHub (Feb 21, 2020):
FWIW, LastPass has a somewhat complex solution for this, though AFAICT, it's not for AD/LDAP per se. I doubt anything like this would get implemented in upstream Bitwarden anytime soon, though.
See the "LastPass Federated Login Services" section:
https://enterprise.lastpass.com/wp-content/uploads/LastPass-Technical-Whitepaper-3.pdf
@alfonsrv commented on GitHub (Feb 21, 2020):
Whoa, easy there. Indeed it was probably naive to assume it would work in a traditional web-app way; should've checked the REST calls earlier – pardon me. Would have been awesome to see it integrated – especially in order to provide a uniform logon experience across an AD infrastructure where convenient management and storage of logins against 3rd party platforms is very relevant, but I agree an LDAP implementation it is likely out of scope given what I know now.
edit: However, not sure how the derived key verification works, but why not let the AD server reply with a similar challenge for verification? If worst comes to worst, there's a "feature" in AD where you can store passwords reversible. Obviously not ideal, but could get the job done, no?
@Crow-Control commented on GitHub (Feb 21, 2020):
Ofcoarse those things are awesome, but lets be realistic: Bitwarden is not meant nor designed to work with centralised user management.
If you want LDAP user control, maybe look at Nextcloud Passwords (although the mobile os support sucks for it), however: as it supports nextcloud user mangement it would support the feature you want :)
@Crow-Control commented on GitHub (Feb 21, 2020):
In that case you need quite complex middleware and my previously proposed middleware solution would be simpler/cleaner.
What you are saying is basically "Why can't I rewrite Bitwarden for LDAP?"... If you have the time and energy you could ofcorase write something that accepts the bitwarden API using LDAP. But it would require MASSIVE redesign if you would take bitwarden_rs as basis.
@ViViDboarder commented on GitHub (Feb 21, 2020):
@alfonsrv something similar to what is in the whitepaper that @jjlin posted could do the trick, but that's a complete architecture change for auth. Client and server.
The whitepaper essentially describes what @Ornias1993 is suggesting. A middleware that they use to interface with AD.
@Crow-Control commented on GitHub (Feb 21, 2020):
@ViViDboarder Addition:
It would also come with a WHOLE host of potential additional security issues that need to be taken care of, so it for sure not anywhere close to "easy".
I would dare to say it might even be harder than writhing bitwarden_rs from scratch.
@repomaa commented on GitHub (Mar 26, 2020):
API Docs! Since not even the official bitwarden server implementation maintains any type of api documentation, it'd be very cool if bitwarden_rs did. It would help alot when developing 3rd party applications. While the routes and payloads aren't that complicated the response data is. It'd be great to have detailed type information about the returned data.
@ndanyluk commented on GitHub (Mar 28, 2020):
Would it be possible to make use of Docker Manifest Lists for a multi-arch image? I do this for all of my images, but I use Travis to automate the builds. For example, I push images to separate repos for each arch (i.e. ndanyluk/prometheus-armv6, ndanyluk/prometheus-amd64) then tag them and push a manifest list to the main repo (in the prometheus example, ndanyluk/prometheus)
@Skeen commented on GitHub (May 1, 2020):
This PR https://github.com/diesel-rs/diesel/pull/1884 has been merged, which could enable PostgreSQL support, by changing
replace_intocalls intoupsertcalls.@goetzk commented on GitHub (May 7, 2020):
Support for SAML would be really good, but I appreciate the extra code to carry might be too much. If there is another supported auth method we could use as an adaptor to SAML I'm interested in hearing about that too.
@ptman commented on GitHub (May 7, 2020):
@goetzk SAML has many of the same problems as LDAP
@goetzk commented on GitHub (May 7, 2020):
Being able to disable users rather than delete them would be really handy. In my case I'm considering writing a (Python) Requests script to create users but if deleting them is the only option that sounds a bit dangerous to script for the exit part of the journey.
@theblackhole commented on GitHub (May 11, 2020):
Add slack integration to the repository so everybody can subscribe to release notifications (only the repo owner, @dani-garcia, can do it : https://slack.github.com/)
If you've never heard of it I explained (the best I could) how it works here : https://github.com/verdaccio/verdaccio/issues/1483
Screenshot of a release notification from Harbor in our slack workspace
@ptman commented on GitHub (May 11, 2020):
@theblackhole You can subscribe to release notifications via Atom. There must be slack bots that can post rss updates. Also, isn't the chat on matrix ( #bitwarden_rs:matrix.org ) and not slack?
@theblackhole commented on GitHub (May 11, 2020):
I didn't know, how do I do that ? I haven't seen any links/button or any mention of Atom feeds in the help website.
The purpose here is not to have a matrix replacement but to add the Slack integration to the repository so everyone, in their own slack workspace, can get notifications for releases (or commits, issues, etc...)
@ptman commented on GitHub (May 11, 2020):
@theblackhole the URL seems to be https://github.com/dani-garcia/bitwarden_rs/releases.atom (look at the html source on the releases page)
@theblackhole commented on GitHub (May 11, 2020):
Thanks for the tip ! I will try to get it working with IFTTT then. I don't know if it will be as good as the official slack integration but it's definitely worth trying :)
@dani-garcia commented on GitHub (May 15, 2020):
It's usually not a great idea to store big files in a database, for performance reasons and that goes doubly so for SQLite. We could potentially store the small attachments in the database, but then having them divided between two places would be worse in my view.
@dani-garcia commented on GitHub (May 15, 2020):
Well the attachments folder can be set using ATTACHMENTS_FOLDER, then you can point it to a mounted network filesystem or similar. For S3 there are FUSE-based software to do it too.
And we still use the disk for the authentication keys, website icons, and config anyway, though that's mostly unimportant from a backup perspective.
@jtcressy commented on GitHub (May 22, 2020):
Has anyone brought up using external tools to implement crypto? E.g. use a cloud KMS solution to manage encryption keys instead of putting .der private keys on the filesystem.
Also, if this could be a configurable interface of some kind, you could use Hashicorp Vault's Transit backend for crypto operations if you don't want to use a hosted cloud service.
@Crow-Control commented on GitHub (May 22, 2020):
I think this is more a misunderstanding than it is a problem with bitwarden. No where in the documentation does it state setting a database means "don't use the harddrive".
It means: "use a dedicated database instead of the sqlite database."
occams razor, basically.
@Crow-Control commented on GitHub (May 22, 2020):
Actually it does.
It states the
ATTACHMENTS_FOLDERfolders and such are relative to the data directory if not set.Which means the stored attachments are too ;)
@Crow-Control commented on GitHub (May 22, 2020):
Statistically speaking no mater how good your documentation is, there is always someone too stupid to understand it. Considering no one hit this issue in years, I think we know where the issue lays.
But indeed lets stop this.
@DheerendraRathor commented on GitHub (Jun 20, 2020):
Request: Please publish bitwarden_rs service as snap package. That will make it really easy to install/use on linux distros without use of any containerization!
@klausenbusk commented on GitHub (Jun 20, 2020):
You can use Docker as mentioned in the README.
@mqus commented on GitHub (Jun 20, 2020):
For all the downvoters: I also don't like snap but I still think that it is a reasonable request for people that do have to use snap or even like it. Please elaborate your dissent instead of simply downvoting without any explanation.
I think docker is not really an alternative for the specific snap usecases, especially if containers were explicitly excluded as a solution by @DheerendraRathor. Its like if you would have asked for a docker image so you don't have to prepare or care about dependencies and I would have told you that you can compile it from source instead.
That said, almost all packaged versions of bitwarden_rs are packaged and hosted on other locations and not here. Nobody can be stopped from building and publishing a snap on their own and it might be reasonable to separate the application from the packaging, so I'm not sure if adding snap build files or something comparable to this repository would be right. This request might be better suited to the forum.
@Crow-Control commented on GitHub (Jun 20, 2020):
@mqus
It isn't about snap.
Supporting packages on your own system, means supporting those... which creates a needles burden on the developer.
If you want to use it customised, building it isn't that hard either.
@mqus commented on GitHub (Jun 20, 2020):
If I understand you correctly then you are saying basically the same thing as I wrote in the last paragraph, meaning that adding a snap package will create additional burden(1) just by needing to support the snap packaging, right? I'm basically with you there, with one small remark: The docker image(s) already are such a package and create a burden (I think at least 1/4th of the issues created are related to docker configuration and packaging issues), so it seems reasonable for people to expect "just one more" package. Additionally, snaps are intended to be packaged directly by upstream developers, so they would fit very well.
Imho the docker files should be in a separate repository (like we expect the snap package to be), but the decision was already made and I don't use docker so I'm probably not in a position to criticize that, especially when I'm not the one maintaining them.
(1) I think the snap burden would not be needless per se but indeed there don't seem to be as many users.
@ViViDboarder commented on GitHub (Jun 20, 2020):
A snap package seems like a valid request, though I'm not sure if there is much interest from existing contributors. You can check out the Wiki to see instructions on building and packaging as well as some existing 3rd party packages that include Arch, CentOS/RHEL, and Debian.
For the time being, if you're not interested in using Docker or compatible platform, you can try those.
One small correction:
A snap is a container. If you want a container free option, you should definitely check out the Third Party Packages.
@Crow-Control commented on GitHub (Jun 20, 2020):
@mqus EVERY added distribution opion ADDS a higher burden on support and development. Just because there already is one distribution option (docker) doesn't change that in any way, shape or form.
Your argument saying because there is docker, more distribution options doesn't mater is illogical and just weirdly structured at best.
That being said:
It's clear you are fishing for debate, thats why people just downvote. Not everyone has time to deal with people looking for debate on irrelevant requests they disagree with. Hence they downvote.
Hence I also ignore your attempt at trying to create a bigger discussion about docker and project structure.
@DheerendraRathor commented on GitHub (Jun 20, 2020):
I don't want to drill further down on this debate - it was just a feature request like any other, and it's okay to be downvoted/upvoted.
Few comments on my requests
Docker container processes use additional RAM. When bitwarden_rs can run within 40M RAM, why do I need container processes taking 100M additional RAM? I'm self hosting it on a cheap ubuntu instance, and by keeping RAM footprint low, I can host additional applications on that server.
And yes, currently I'm building from source on my laptop and transferring binaries to hosted instance. I added feature request so deployment/update process can be streamlined. Right now, I'm subscribed to release notifications and will update my hosted app with new releases coming in.
And I'm against creating my own (or third party) packages - it creates trust issues. I would happily install packages published from an official source, but won't install from third party and neither will like anyone else to trust my package for a password manager.
So re-wording my request:
Please publish bitwarden_rs service binary on an official channel (like github packages). That will make it really easy to install/use on without use of any containerization!
@klausenbusk commented on GitHub (Jun 20, 2020):
You could try another container engine. Podman comes to mind.
@dirtycajunrice commented on GitHub (Jul 24, 2020):
I saw the timestamp addition which is awesome! To piggyback that i would like to request formatting options as text or json. When using json logging its easier to tag logs with things like promtail :)
@iamvtor commented on GitHub (Aug 6, 2020):
Limiting who can export passwords would be useful. Or even just the ability to disable it entirely.
@quentinus95 commented on GitHub (Aug 12, 2020):
Bitwarden just announced support for SSO: https://bitwarden.com/blog/post/bitwarden-password-manager-login-with-sso/
Does this unofficial version has any plan to add support for this feature as well?
@Crow-Control commented on GitHub (Aug 13, 2020):
I think we should wait till we have an actual design draft to review and/or a code audit.
my best bet would be that this feature is mostly a client side feature...
@Crow-Control commented on GitHub (Sep 11, 2020):
I was wrong. Its also server side supported.
(And I was an idiot, because SAML requires server-side support by-design >.<)
@dani-garcia this is a list of server-side changes to support SAML done by bitwarden official:
https://github.com/bitwarden/server/commits/fd6b10df564778ea73c00e8dcecc00aa74c5eb7d/src/Core/Enums/SsoType.cs
Technically speaking:
It's a glorified SAML reverse-proxy in front of Bitwarden, but integrated.
It does not change the fact one needs a master password to actually enter, but adds a login step.
I think this is actually more doable than it seems at first glance 👍
@dr-bonez commented on GitHub (Sep 18, 2020):
Feature Request:
Federation.
My coworkers all run self-hosted bitwarden_rs servers, but we want to share some passwords, so we have an organization account on one of them to share passwords with. Then, in order to use those, we have to change our backend url to the server with the org temporarily.
It would be nice if an organization account could be synced across servers. When adding a member to an org, you could optionally add a different backend url and it would sync the passwords to that user on that server.
SOCKSv5 proxy support for federation would also be nice to have.
@ptman commented on GitHub (Sep 21, 2020):
@dr-bonez I wouldn't like to let federation anywhere near my password storage. Additionally, I think this is something that bitwarden_rs cannot really do without upstream bitwarden solving it.
But as a solution to your problem, it seems like bitwarden clients have signing on to multiple servers simultaneously in the roadmap (see Client Profiles)
@ptman commented on GitHub (Sep 21, 2020):
Support for Event Logs would be great for organizations.
@dr-bonez commented on GitHub (Sep 21, 2020):
The passwords would never be in plaintext so federation as an available feature doesn't seem like much of a risk. But client profiles that support multiple backend servers would do the trick too.
@symphorien commented on GitHub (Sep 26, 2020):
Localization for emails.
@ccakes commented on GitHub (Sep 28, 2020):
Support for authenticating users via an existing JWT passed in via a header would be nice. Looking to deploy this where SSO is managed and backend apps get passed a JWT which they can then verify to identify the current user.
Would be nice to have that support here also. An example of an app that supports this is Redash (see the
REDASH_JWT_*environment variables).@Crow-Control commented on GitHub (Sep 28, 2020):
@ccakes This has been discussed before: This can't be done.
The server doesn't authenticate based on username and password or token. the client does based on being able to decode a snipped from the server.
@ccakes commented on GitHub (Sep 28, 2020):
@Ornias1993 Ah ok - no problem. I did look through the issues for something similar but must have missed it. Thanks for the quick response!
@Crow-Control commented on GitHub (Sep 28, 2020):
No problem, basically the same issues with SAML/SSO we had already:
While bitwarden implemented SAML auth, it's only on-top (or in front rather) of the bitwarden auth (so you need to just add 2 credentials instead of one). Simply because you can't decode bitwarden passwords with sending SAML/SSO/JWT(in your case) credentials, because the server isn't authoritive.
Simply put: We don't trust the server to be trustworthy enough to process passwords,
@Thomas2500 commented on GitHub (Oct 11, 2020):
Feature request: Add custom CA certificate to trust store
I have stored multiple internal addresses within my password store and bitwarden_rs tries to fetch the favicons of the internal services as wanted. Because I am using not a publicly trusted CA for internal services, bitwarden_rs fails to fetch content.
I think the same problem could occur if a self-signed certificate/internal issued certificate is used for SMTP.
A possibility would be to add custom (root) certificates within the admin interface which are additionally trusted. This would allow bitwarden_rs to make secure connections without the use of publicly trusted certificates and without disabling certificate validation.
As a workaround, I mapped the certificates of my host into the container which extends the trusted certificate store and let
update-ca-certificatesexecute after container creation.@davidus05 commented on GitHub (Oct 11, 2020):
Feature request: IP restriction for accessing the admin panel
It would be really nice to have an option to block all networks, excluding the networks on the list. That would increase the security of the panel, since there isn't 2FA available for it yet.
Example: block all networks, excluding the internal network 192.168.0.0/16
@bjo81 commented on GitHub (Oct 11, 2020):
@davidus05
Simply restrict the /admin location in the reverse proxy?
@BlackDex commented on GitHub (Oct 11, 2020):
@davidus05, i would go with @bjo81 on this.
The same goes for API rate limiting etc..
Most reverse proxies are much better in this and have a better track-record for having good blocking and security functionality.
So i think that is the best way to go.
Maybe somewhere in the future we can add it, but for now i don't think it is a priority since reverse proxies can solve that.
@arejaytee commented on GitHub (Nov 10, 2020):
I can't seem to find this but if there is no option like the old LP security challenge grading your passwords and etc, would be great to have that from within bitwarden_rs
@Crow-Control commented on GitHub (Nov 10, 2020):
Please note: Bitwarden RS is only the backend server.
All things in the UI (like security checkmarks, tests etc) are not developed by BitwardenRS
@Eviepayne commented on GitHub (Nov 14, 2020):
One thing I'd really like is an easy way to setup connecting to an SMTP relay.
Does the env/global.override.env work? I never got it to work.
@VictorElHajj commented on GitHub (Nov 17, 2020):
Add compatibility with docker secrets, so allow using ADMIN_TOKEN_FILE and DATABASE_URL_FILE etc so that secrets can be kept separate from the docker_compose.
@yegle commented on GitHub (Nov 20, 2020):
If it makes implementing SSO easier, it might make sense to support an identity aware proxy like https://pomerium.io
@Crow-Control commented on GitHub (Nov 20, 2020):
@yegle You CAN NOT do true SSO with bitwarden, not bitwarden(tm) and not bitwardencore.
You ALWAYS need to login with your bitwarden credentials, it's by design. Simply put: the CLIENT does the authentication, not the server, there is not way bitwardenRS (The server) can support true SSO.
@Eviepayne commented on GitHub (Dec 1, 2020):
I've run into the same issue. I think the global.override.env only works on the official CLI only bitwarden.
There should be an SMTP configuration implemented so we can use the email functions on home networks where smtp ports are blocked.
@ViViDboarder commented on GitHub (Dec 1, 2020):
@VictorElHajj take a look at this comment for a possible solve for what you're trying to do. https://github.com/dani-garcia/bitwarden_rs/issues/246#issuecomment-495315985
@BlackDex commented on GitHub (Dec 2, 2020):
@ViViDboarder & @VictorElHajj, this should be available now via this PR #1244 . So using the
testingrelease from docker hub would have this feature.@pieterhollander commented on GitHub (Dec 17, 2020):
I've just contributed a Logrotate example. Therefore it might be possible to mark Log rotation / management #305 as fixed.
I also noticed that somebody contributed an example for migration from SQLite to PostgreSQL, so Easy migration, from SQLite to other two options --> SQLite to PostgreSQL could also be marked as done.
@SebastianS90 commented on GitHub (Jan 4, 2021):
The official Bitwarden Server / Web Vault will soon support an Emergency Access feature to grant a trusted person access to your vault in case of death or other unresponsiveness, see the Bitwarden feature request.
It would be awesome for bitwarden_rs to support that feature as well.
@sangdrax8 commented on GitHub (Jan 13, 2021):
Is there a way to track roadmaps for some of these requests? I see that LDAP user invites has been implemented, but I am really interested in getting the groups to sync with LDAP like upstream bitwarden connector can do. I can handle ensuring my new users HAVE an account, but would really like to have bitwarden_rs pull from my source of truth for groups, so they can be used for access controls on collections.
@ViViDboarder commented on GitHub (Jan 13, 2021):
@sangdrax8 it's been discussed a bit in the past. There is the option of expanding the admin API and the current LDAP sync service, or (more preferable) expanding the Bitwarden_rs APIs to support the official Directory Connector. It maybe more work to do the latter, but it would allow better long term support.
Just did a little digging. It looks like the Directory Connector POSTs a collection of users by org to
/organizations/{id}/import. That API is defined here in the original controller.@sangdrax8 commented on GitHub (Jan 13, 2021):
Just out of curiosity, as I am not a rust developer my self. Is there a bounty program if I wanted to try and see if we could support some development on that API implementation? There is a chance we could support with developer cycles, but I would have to check and see if I could get that approved too.
@gked commented on GitHub (Jan 27, 2021):
I had trouble connecting to bitwarden server on Embassy from ios and windows bitwarden apps. With some research, I found this thread. I was wondering whether you have some idea on implementation timeline?
Thanks!
@jjlin commented on GitHub (Jan 29, 2021):
https://community.bitwarden.com/t/tor-support-for-ios-and-android/12721/13 indicates this feature requires client support only, so there is nothing to be done on the bitwarden_rs side.
@neojp commented on GitHub (Feb 7, 2021):
In the admin panel, I'd like a way to see if a registered user has verified their email and a way to "sudo" force verify it for them.
I registered my first user without setting up my SMTP settings and had
SIGNUPS_VERIFY=false. Once I enabled it, I'm having issues getting the verify email from working and can't access my account.@thelittlefireman commented on GitHub (Feb 10, 2021):
WIP :) https://github.com/dani-garcia/bitwarden_rs/pull/1377
@jjlin commented on GitHub (Feb 16, 2021):
@Germs2004 bitwarden_rs is a backend API implementation. You'd have to suggest any client changes to the upstream Bitwarden project.
@ViViDboarder commented on GitHub (Feb 16, 2021):
@Germs2004 as @jjlin said, that would need to go upstream. Here's a link to the Bitwarden forum for feature requests.
@Germs2004 commented on GitHub (Feb 16, 2021):
Sorry, I thought the web-based GUI was part of the server and something that BitwardenRS has implemented in Rust. If I'm mistaken, I apologize and you can please delete those requests from this thread.
@jjlin commented on GitHub (Feb 16, 2021):
bitwarden_rs bundles the upstream web vault with some very minor modifications, but isn't going to make large changes like what you're requesting. I'm not able to delete your comments, but you can delete them yourself.
@Germs2004 commented on GitHub (Feb 16, 2021):
Do upstream web vault changes automatically come down to BitwardenRS when you release future versions? I'd like to understand better how the RS project works - is there some article somewhere that explains it?
This text on the RS project's readme confuses me now:
--Edit: I found this list of web vault patches. That seems to answer my question. Looks like you pull their latest web vault code, patch it to work with the rust code, and include that modified version with the RS docker image. So it looks like upstream web vault changes do come down to the rs version.
@dumblob commented on GitHub (Feb 17, 2021):
Hi, we're trying to slowly move to NextCloud as our main "dashboard" including communication (email, chatops, customer support, etc.). To make that happen, we need a very good support for working with credentials, keys, etc. for every user in our medium-size enterprise.
Do you think there is any integration needed for running bitwarden_rs along with NextCloud on the same machine? We're currently testing https://github.com/downtownallday/cloudinabox for half a year, but it still has too many sharp edges and the sharpest one is credentials management (yeah, all the NextCloud apps for credentials etc. feel like a joke compared to bitwarden).
We didn't try bitwarden_rs yet, but there are at least a few inevitable things to keep in mind:
@mcastorina commented on GitHub (Feb 21, 2021):
Hi, thanks for making this awesome self-hostable server!
It would be cool to have automatic password rotation (or even one-click). What are your thoughts on this?
@hopepanwei commented on GitHub (Mar 4, 2021):
Hope to be able to create multi-level folders for more granular management of password groups
@mprasil commented on GitHub (Mar 10, 2021):
@hopepanwei you can already do that. See docs here
@jyundt commented on GitHub (Mar 11, 2021):
Are there any plans to implement the new Bitwarden Send functionality?
@dani-garcia commented on GitHub (Mar 11, 2021):
Yeah, this one's of personal interest to me, so I'll take a stab at implementing it over the weekend.
@mikeburgh commented on GitHub (Mar 14, 2021):
For send, any thoughts on separating the collection of the files from the main Bitwarden service ? I like the idea of send, just not sure about the risks of exposing the full service to the public internet.
One thought I had was if via admin you could specify a separate port for the send collection routes an different url to copy into the clipboard for the send collection link you could then cover that with a reverse proxy or similar to just expose send collection.
@immanuelfodor commented on GitHub (Mar 14, 2021):
With a reverse proxy, I feel it could be done even if there is no new ports added. It should work with the main domain for compatibility reasons but you can always point a new domain to the existing service and proxy only a subpath to this new domain.
@apx19 commented on GitHub (Mar 15, 2021):
Would it be possible to implement an option for increasing the limit of passwords stored in password history?
It seems like the limit is there for no reason. I may be wrong but it would be nice if there was some way to change it.
@viyh commented on GitHub (Mar 16, 2021):
A great feature would be the ability to export a specific collection (or even a set of collections), instead of just the entire vault or nothing.
@BlackDex commented on GitHub (Mar 16, 2021):
For a feature like this you need to go to https://community.bitwarden.com/c/feature-requests/5
@BlackDex commented on GitHub (Mar 16, 2021):
I think that would be complex on our side because the clients only return a maximum of 5. So also for this i think best place would be: https://community.bitwarden.com/c/feature-requests/5
@marq24 commented on GitHub (Mar 23, 2021):
would you mind to update the wiki in the meantime? Currently 'Bitwarden Send' is listed as Supported Feature of bitwarden_rs (here: https://github.com/dani-garcia/bitwarden_rs/wiki) TIA
@BlackDex commented on GitHub (Mar 23, 2021):
I added a very small note to it that it is currently only in the
testingtagged image.@LookedPath commented on GitHub (Mar 26, 2021):
Would it be possible to add folders to organizations vaults?
Another thing that I noticed is the fact that it's impossible to search for a folder name, how hard would that be to implement?
@BlackDex commented on GitHub (Mar 26, 2021):
That is not something we can add, for requests like this you need to be with bitwarden.com (Upstream).
https://community.bitwarden.com/c/feature-requests/5
For searching there is a wiki: https://bitwarden.com/help/article/searching-vault/
@unalkalkan commented on GitHub (Mar 29, 2021):
Since this is a self hosted project, would it be a proper feature request to increase the default Send maximum file size? Maybe from an environment variable?
@BlackDex commented on GitHub (Mar 29, 2021):
That's not possible since the clients have these limits set also.
We would need to fork the clients for that to work
@unalkalkan commented on GitHub (Mar 29, 2021):
Then I think I'll propose it on the upstream project to see if they are willing to implement something where the server passes the limit to clients in some way. Is there any similar scenario where server passes this kind of configuration the clients?
@BlackDex commented on GitHub (Mar 29, 2021):
I don't think they are willing to do that. First, send with files is a premium feature. And, i think there are some encryption limits, because the same limit is also for attachments.
@TechKnowCase commented on GitHub (Apr 3, 2021):
Works perfectly on ungoogled Chromium. Thanks for you work, @dani-garcia!
(I'm using docker)
@beppe9000 commented on GitHub (Apr 22, 2021):
can we have official docker-compose.yml example file ?
@attzonko commented on GitHub (Apr 22, 2021):
For your reference here is my working docker-compose bitwarden_rs service entry, I use Traefik 2.0 as the reverse proxy:
@beppe9000 commented on GitHub (Apr 26, 2021):
Thanks!
@beppe9000 commented on GitHub (Apr 26, 2021):
Do you have any idea where I can add some custom css for the web gui (and hopefully for the app) in a non-destruptive way (e.g. mounting a docker volume)?
@pepa65 commented on GitHub (Apr 26, 2021):
We just patch the css here in the docker container:
/web-vault/app/main.*.css(Not sure about the value of the*for every kind of container...)@beppe9000 commented on GitHub (Apr 26, 2021):
I added it as a proposal in the web-vault repo because it's related more to it than bitwarden_rs itself.
I don't know about customizing SCSS, tho. Because of the building steps involved it would be a little more difficult to setup a
custom.scssfile. I don't think it's impossible, but that would require recompiling everything on change.Change detection would happen in the docker image, on boot or every once in a while (store and compare
custom.scsshash, recompile and repeat if different from storage).So supporting Custom SCSS would require changes to the docker image, whereas Custom CSS should not require more than a line of text patched in the final html/css and an empty file.
@JerryHan3 commented on GitHub (Apr 29, 2021):
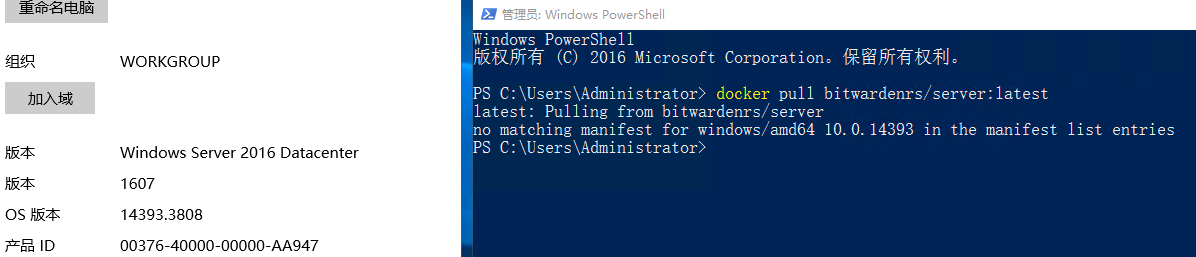
Really hope that you can support Windows Server 2016. I tried to pull the file from docker, and an error popped up and I reckon it's caused by compatibility issues. Here's a screenshot of the error and the information of my server's system.
@BlackDex commented on GitHub (Apr 29, 2021):
You probably need to setup docker to use Hyper-V to run the container within a Linux Hyper-V VirtualMachine.
We currently do not build Windows binaries, and i'm not sure if we want to support that.
@beppe9000 commented on GitHub (Apr 29, 2021):
I was able to directly build from sources in windows server 2016, maybe it's faster/easier ?
@BlackDex commented on GitHub (Apr 29, 2021):
Yea i think that would be easier indeed. No container needed. But with new version you need to compile again, if that is not an issue, i would suggest that.
@beppe9000 commented on GitHub (Apr 29, 2021):
did the repo and docker images just change name?
@attzonko commented on GitHub (Apr 29, 2021):
Yes it appears so: https://github.com/dani-garcia/vaultwarden/discussions/1635
@EliRibble commented on GitHub (Apr 30, 2021):
I'm interested in discussing what it would take for me to implement SSO to Keycloak - should I discuss that on this issue, or create a new issue?
@BlackDex commented on GitHub (Apr 30, 2021):
If Keycloack is supported via the SSO feature from bitwarden, then a PR with an implementation feature compatible with upstream would be the way to go. See https://bitwarden.com/help/article/about-sso/
@mpember commented on GitHub (May 6, 2021):
Is it possible to have "Select All" / "Select None" functionality, making it easier to make bulk changes to a whole folder of entries (e.g. A user that has a folder of items-related to a specific job / client may want to share every item in that folder to an Organisation).
@BlackDex commented on GitHub (May 6, 2021):
This place is not really the right place to ask these questions, the forum or discussions would be better.
I'm not sure what you mean with a folder of e-mails. But if you just mean a folder within the web-vault, then you can just click on the gear icon at the top right, click
Select All, and after that use that same gear icon and clickShare Selected@mpember commented on GitHub (May 6, 2021):
I apologise for the confusion. I meant to say "items", not "emails".
That was the functionality I was looking for. I clearly overlooked the functionality because I wasn't yet fully familiar with the UI. I am accustomed to having the select all/none option visible in the main interface (rather than under a menu) and normally associate a "gear" icon with accessing 'settings'.
@MyNameIsOka commented on GitHub (May 7, 2021):
Hello everybody,
sorry for pestering but is there any update on the emergency access functionality? This would be a very convenient feature.
Alternatively, do you have any suggestion how to handle this use case currently?
Thanks a lot!
@BlackDex commented on GitHub (May 7, 2021):
Well, you can look at the PR #1377, and see that there still is some fine tuning needed for it.
@MyNameIsOka commented on GitHub (May 7, 2021):
Sweet, so it's actively being worked on! Looking very forward to this feature!
@matbrgz commented on GitHub (May 10, 2021):
The SSO implementation could help this project bring enterprises to this. I'm heavily considering start use this after SSO feature.
@beppe9000 commented on GitHub (May 10, 2021):
What about using Vaultwarden as an SSO provider ? If SSO gets implemented the step is little to add this.
@HenkVanMaanen commented on GitHub (May 18, 2021):
My colleague found a hack to get folders in organizations vault.
First create the base collection, e.g.
Mail accounts. And then you can create a folder by naming the folder BASE_NAME/FOLDER_NAME, e.g.Mail accounts/Marketing. So putting a slash in between as if it's a path.@mr-manuel commented on GitHub (May 19, 2021):
Hello to all :)
It would be nice to have this features also in Vaultwarden:
Add filter to only display personal items (hide any items that belong to a organization)
Show collection and folder ownership of an item in list view
@ibotty commented on GitHub (May 20, 2021):
I am interested in contributing OIDC login. I am a little familiar with OIDC but not with bitwarden or vaultwarden. What OIDC flow does bitwarden use?
@omueller commented on GitHub (Jul 2, 2021):
Hi @dani-garcia, if you have some time, could you please have a look at my comment a few weeks ago under https://github.com/dani-garcia/vaultwarden/discussions/1623#discussioncomment-845672 ? (tl;dr: groups-support implementation, sponsored by vaultwarden users maybe ?) The alternative described in this ticket ("use different organisations") is not really a good option (https://bitwarden.com/help/article/about-groups/). Thanks & a nice week-end to you!
@technowhizz commented on GitHub (Jul 11, 2021):
@ibotty Are you able to implement a google-sso PR?
I truly think that adding SSO/SAML/OIDC to this would make this THE ONLY free password manager with SSO as all other solutions are paid.
@varac commented on GitHub (Jul 13, 2021):
I'd be happy if Oauth/OpenIDConnect would be implemented because it's the main blocker from including it in https://openappstack.net/
@technowhizz commented on GitHub (Jul 13, 2021):
@everyone who here is able to help develop the oauth2/sso plugin for vaultwarden?
Let's get this done
Like this comment if you're down to help code it
@ibotty commented on GitHub (Jul 16, 2021):
@technowhizz I am willing to work on that, but would not specifically target google OIDC. It will be possible if the generic support is there though. I will still need some pointers on where to start though. I cannot allocate enough time to dig deep without any pointers.
@colinfrei commented on GitHub (Jul 17, 2021):
Since Github has Discussions now, it might make sense to close this thread and allow Feature Requests in the Discussions tab.
That'd allow more focused discussion about each feature request, as well as voting on them
@varac commented on GitHub (Jul 28, 2021):
@ibotty awesome ! We'd also be in favor of generic OIDC support to use it together with hydra.
Hope anybody will support you to get started soon 🤞
@grawlinson commented on GitHub (Aug 7, 2021):
The
rustup-toolchainfile seems to be legacy.It may be worth switching over to
rustup-toolchain.tomlat some stage.@Taker567 commented on GitHub (Aug 20, 2021):
A question about this point:
Support official LDAP directory-connector
This shows up as supported in the list above, however using the official directory-connector (https://github.com/bitwarden/directory-connector) requires you to login to your backend using a client ID and client secret, not email and password, this doesn't seem to be currently possible in vaultwarden. Is issue 1250 supposed to cover this requirement?
@BlackDex commented on GitHub (Aug 20, 2021):
You need to use an older version with Vaultwarden.
V2.9.2 is the latest version you can use, also see https://github.com/dani-garcia/vaultwarden/wiki#supported-features
@ViViDboarder commented on GitHub (Aug 20, 2021):
@BlackDex I think you made a typo. It’s that you need to use an older version of the Bitwarden directory connector. Not older Vaultwarden. Unless I’m reading something incorrectly.
@BlackDex commented on GitHub (Aug 20, 2021):
@ViViDboarder, i say with Vaultwarden, not of Vaultwarden.
@ViViDboarder commented on GitHub (Aug 20, 2021):
Ah. Indeed you did. My bad. Well, at least we've clarified for anyone else suffering from reading comprehension issues like me. 😉
@technowhizz commented on GitHub (Aug 24, 2021):
Any one down to help with pointers? :)
@ibotty to start theres an oauth module for rust here: https://docs.rs/crate/oauth2/4.1.0
@vivithecanine commented on GitHub (Sep 21, 2021):
It would be nice to have a container config that bundled a proxy so that we could have an all-in-one container that provides static content hosting + the web application + websockets.
@Miarka24 commented on GitHub (Sep 22, 2021):
Hi, I first have to say in my two days investigating opensource passwordmanagers for my company vaultwarden is clearly in the lead right now, I have compared it to Passbolt and PSONO, we are a small company but secure passwords and password management is getting more and more important.
I have noticed two things I would love to have, as far as I can say those are not implemented in bitwarden either.
Ultimately both try to achieve a similar thing: prevent users to delete entries but allow them to update entries/passwords.
Considering company Passwords and sharing them with users added to the company there are currently two options for normal Users: "hide passwords" and "read only".
I´d love an additional option "update", this would allow users to update passwords but prevent them from deleting entries.
The other option is similar, but eventually easier to implement, keep everything as is but prevent normal users from accessing organizations recycle bin, this way it is not possible for a user to completely remove an entry. Managers/Admins would have 30days to recover deleted entries.
Maybe I have missed something and what I am requesting is already possible in some way, if so I´d be happy for some pointers :).
MfG/Best regards
Jonas Stunkat
@alfonsrv commented on GitHub (Sep 22, 2021):
Likely not to be implemented @Miarka24. Use database backups.
@Miarka24 commented on GitHub (Sep 22, 2021):
Well backups are the bread and butter of course, but having this option wouldn´t hurt.
I am thinking about cases where you have many MANY passwords but some of them you dont use regularly, if a password like this gets deleted from the recycle bin too, it would be hard to notice and looking through the backups could become a pain.
I have read there is a feature request for an audit log, that could help if deletions are logged.
@NoseyNick commented on GitHub (Sep 22, 2021):
Seeing as you mentioned backups...
I assume it is almost by definition impossible to carefully restore individual passwords from a backup, because they are all so nicely encrypted you wouldn't even know which is which, never mind which to restore? How about restoring individual users and/or organizations one at a time? ... but even then, presumably "restore entire user to a point in time" with obvious risk of losing ones that were added after the backup as well?
@BlackDex commented on GitHub (Sep 22, 2021):
@Miarka24 @NoseyNick.
I think point 1 is more something for upstream Bitwarden.
There need to be client side support for that too.
Point 2, depending on what rights you give people to the org. You can give them read only access, while they can still share passwords and use them they can't delete them for an org.
Building both options into Vaultwarden would require significant work and new special options on the server side which we try to minimize as much as possible to keep as close as possible to Bitwarden.
Regarding restoring separate entries, that is in theorie possible, as long as the security keys aren't changed of the org, or for users, if they didn't rotated there key or changed there password.
Having backups is probably the best thing to do. You can just start a separate Vaultwarden container using the backup and try to find it.
@NoseyNick commented on GitHub (Sep 22, 2021):
Aha! Hadn't occurred to me but really good point, and certainly sounds easier than meddling with individual database records and stuff. Thanks!
@Miarka24 commented on GitHub (Sep 27, 2021):
@BlackDex
I don´t know about client support, wouldn´t it be the same as read-only? Even the same error message could be applied.
Regarding the code changes, that may be true I´didnt look too deep into the code.
Read-only is definitiv an option, but it has its own problems, if a user has the password, the user probably can change the password but will not be able to change it in the database. It would be similar to a deleted password or even worse.
But regardless, if this project is set up to follow bitwarden closely, I will respect that and hope bitwarden will introduce something similar in the future.
@S1M8N commented on GitHub (Oct 3, 2021):
Hello,
This is very important :
Do you have any idea when the configurable option will arrive ?
Thank you for your information
@JBFUK commented on GitHub (Oct 7, 2021):
Live sync for iOS devices please.
@BlackDex commented on GitHub (Oct 7, 2021):
I am a bit against that. Because that could be used as a DoS feature. If i know your username and your host, i will just try random passwords and bam your account is locked.
I would suggest to use something like Fail2Ban, or some kind of WAF provided by the reverse proxy.
@BlackDex commented on GitHub (Oct 7, 2021):
Probably not going to happen in the near future.
This needs a API-Key from Bitwarden, and also the usage of there services.
@NoseyNick commented on GitHub (Oct 7, 2021):
I am amazed at how few people recognise this. I remember a previous employer proudly announcing that your account will be locked out after 3 login failures, and you'd need to ask IT Helldesk to unlock you. "For security reasons". My immediate question was "So how long until someone writes something that fails to log in as [CEO]@[COMPANY].com every minute? This is a SECURITY feature?"
Well so is the "locked safe dropped to the bottom of the mariannas trench" thing but come on!
However some (extremely stoopid) regulatory frameworks require this functionality, which is presumably why upstream has implemented it. Best compromise is usually "lock for N minutes and then unlock"
And in the case of [CEO]@[COMPANY].com, or anyone else @[COMPANY].com, it turns out that it doesn't need a skript kiddie to do this maliciously, just someone, almost everyone, including [CEO], to change their password but forget to update it on some email client somewhere that checks for new mail every N minutes. (Or in our case presumably the BitWarden client on their phone / laptop / other desktop)
... and THEN they learn that IP-specific fail2ban / similar is a better idea after all, so it doesn't block the devices you have updated, and almost certainly meets the same regulatory requirement. 🙈
@ninjamonkey198206 commented on GitHub (Oct 14, 2021):
I deleted my previous request, as I worded it I correctly.
The ability to create nested folders and move passwords between them inside organizations would be a wonderful addition.
It would also be wonderful to be able to share entire folders, not just individual entries with organizations, though that would rely on the folder capabilities.
Edit: After reading other posts and comments I realize this is likely an upstream thing. They essentially have to functionally have organizations as shared vaults rather than a separate function.
@hellfish2 commented on GitHub (Oct 20, 2021):
Please consider adding granular access

@p3lim commented on GitHub (Oct 20, 2021):
Please considering supporting the Admin Password Reset feature, including the organization policies for automatic (forceful) enrollment.
@zocimek commented on GitHub (Oct 26, 2021):
Please consider adding otp configuration within the secret fields in format
otpauth://TYPE/LABEL?PARAMETERS:otpauth://totp/<label>?secret=<secret>&digits=<digits>&algorithm=<algorithm>&issuer=<issuer>&period=<period>The same works with other password managers e.g Enpass
@fyrak1s commented on GitHub (Nov 1, 2021):
Hi, I would like to request a feature to support deduplication of password entries. This is the major pain point for me with vaultwarden.
I've imported passwords from many different browsers and sources and this has created a mess, in which I have every password duplicated about 5 times.
Also it is not easy to manually bulk delete or even compare entries. It is an impossible task for hundreds of passwords to review each entry manually and delete the dupes.
Other pw managers like lastpass do this automatically.
So far there are only workarounds to this problem e.g. https://hwrrobotics.com/2020/11/02/duplicate-password-remover-for-bitwarden/ or https://gist.github.com/giabao/f4c3de705f1d7f2c1fd0cde02e7b841d
And I am not even talking about deleteting/tyding up similar entries (which would be nice), but simply removing obvious 1:1 dupes.
@BlackDex commented on GitHub (Nov 1, 2021):
That is something for the clients. See https://community.bitwarden.com/t/duplicate-removal-tool-report/648
@Luis-Lourenco commented on GitHub (Nov 7, 2021):
Hello Sir, how are you?
Its possible to have a file vault inside the Biwarden_RS? if its , how can I configure ?
kind regards, Luis Loureço
@romu70 commented on GitHub (Nov 11, 2021):
Could you please add the wait-for-it script in the Dockerfile, to poll the availability of the DB? The current container stops when the DB is not available. It would be great if it could simply wait.
@BlackDex commented on GitHub (Nov 11, 2021):
@romu70 If you are using docker-compose you can configure it to have vaultwarden depend on the database container.
You can also configure the
DB_CONNECTION_RETRIESvariable to be increased, every retry is a second.Or you can add a script like that your self by following this: https://github.com/dani-garcia/vaultwarden/wiki/Starting-a-Container#customizing-container-startup
@lzinga commented on GitHub (Nov 11, 2021):
I use vault warden by myself and don't need any organizations, it would be nice to be able to disable organizations and have it remove the prompts for it -

As the only individual that will be using my locally hosted vault I will not be needing organizations any time soon and it would be nice to remove it from the interface.
@p3lim commented on GitHub (Nov 11, 2021):
@lzinga the web interface is not made by vaultwarden, it's the official one, vaultwarden simply includes it.
See https://github.com/bitwarden/web and https://github.com/dani-garcia/bw_web_builds
If you yourself want to hide it, use an extension like stylus.
@LecrisUT commented on GitHub (Nov 30, 2021):
First of all, could this issue be converted to a discussion so that the feature request discussions can be viewed as threads. This format is so unwieldy IMO.
Otherwise I have a feature request and design I would like to post for consideration:
One/Two-way sync with keepass using asymmetric encryption
Problem being solved
Securely synchronizing a user's selected passwords with a hosted keepass database. Primarily this helps with sharing passwords with users across these different infrastructures and offer the user a trusted backup plan.
Design
.kdbxshould be uploaded to, preferably via WebDAV or S3.Why the extra encryption?
Other issues it can help with
Depending on which part is being tackled, partial integration of this would help with:
@BlackDex commented on GitHub (Nov 30, 2021):
@LecrisUT there is a nice https://github.com/dani-garcia/vaultwarden/discussions/categories/ideas discussion categorie where you could have posted this of course.
Maybe locking this thread and pointing people to there is a good option. It was mostly intended to serve as a single location with an overview of all requests.
Regarding the post it self.
Vaultwarden does not encrypt or decrypt it self (except for jwt tokens or ssl connections). Adding that kind of a layer upon Vaultwarden would make it more harder to maintain. Also, we try to keep as close as possible to Bitwarden as we can, so I think these kind of requests are out of scope.
@BlackDex commented on GitHub (Nov 30, 2021):
This issue is getting a bit large, and since there are discussions available for a while I'm going to lock this topic.
The first post will still be updated when needed.
If there are any feature's you currently miss, and are not mentioned in the first post already, please create a new post with your idea/request here: https://github.com/dani-garcia/vaultwarden/discussions/categories/ideas .
Thanks for all your ideas and support!